|
Complete Suite of Embedded Web Development ToolsStandalone Tools for Embedded Development
IoT Protocols
Quick Look
|

“IoT Messaging made secure, trusted, and easy” Source Code | No RoyaltiesIntroducing SMQ - the real-time device management solution for one to millions of devices. Based on industry-standard protocols, SMQ can be integrated into any device, from tiny to cloud-based servers. With user interfaces available in HTML5 and Java (including Android), SMQ makes it easy for developers to deliver top-notch management capabilities for their products. As an enterprise-ready IoT protocol, SMQ is perfect for large-scale product control and management. Plus, it's quick and cost-effective to implement. Upgrade your device management with SMQ today! |
Thanks to its strong security measures, SMQ is perfect for modern IoT solutions. Like MQTT, SMQ exchanges messages through a broker, and the SMQ broker is included in the Barracuda App Server. It can run on various platforms, from embedded devices to cloud servers, and supports clustering for horizontal scaling and redundancy. Plus, SMQ's clustering feature allows bridging between an embedded device on a private network and an online cloud server.

Security is a top priority in any modern IoT solution, and SMQ has been built with security in mind from the ground up. It offers strong authentication and message authorization and is designed to be invisible to port scanners. Trust SMQ to keep your IoT solution secure and efficient.
MQTT and SMQ are messaging protocols used in Internet of Things (IoT) applications. While both protocols are used for (IoT) communication, they differ in design and intended use cases.
MQTT (Message Queuing Telemetry Transport) is a messaging protocol that is designed for telemetry and data exchange between devices. MQTT uses a publish/subscribe model, where devices publish messages to a broker, which then distributes the messages to all subscribed devices. MQTT is commonly used for sending telemetry data to a (cloud) database for processing and analysis.
SMQ (Simple Message Queue) is a messaging protocol designed specifically for device management. SMQ uses a publish/subscribe model, with the addition of one-to-one messages and a sender's ID, allowing for more fine-grained control over which devices receive specific messages. SMQ is typically used for device discovery, configuration, and management, making it useful for tasks such as firmware updates, device configuration, remote device control, and synchronizing multiple UI instances.
In summary, while MQTT and SMQ use a publish/subscribe model for messaging, their design and intended use cases differ. MQTT is designed specifically for telemetry and data exchange, while SMQ is a messaging protocol designed specifically for device management, with a publicly available specification, source code for many platforms, and a simple API.
Customer use case: Car Charger IoT Solution Powered by the SMQ Protocol
SMQ makes setting up your own IoT servers and hosting your own services simple. Whether you want to host your services online or on your own private network, SMQ makes it easy and cost-effective.
Make a positive impact on the environment and reduce your IoT cloud service costs! SMQ is a more environmentally friendly alternative to CPU-intensive software that requires numerous data centers. For more information on setting up a sustainable IoT solution with SMQ, check out the tutorial How To Set Up an Environmentally Friendly IoT Solution. Do your part for the planet and your bottom line by choosing SMQ for your IoT needs.
To illustrate how easy it is to set up SMQ services on the Internet, check out our elastic SMQ cluster demo. You may use SMQ with traditional cloud service providers such as Amazon (AWS) and Microsoft Azure; however, SMQ is very flexible and lets an IT person install the services on virtually any type of server.
The above figure depicts an SMQ cluster with four brokers; however, our online cluster example consists of two brokers. The two computers provide horizontal scaling and high-grade fault tolerance. The DNS for the domain name simplemq.com translates to two IP addresses. We have also configured the DNS so you can go to a specific server by entering https://nodeN.simplemq.com, where N is 1 or 2. See the Interactive High-Availability IoT Cluster Tutorial for details.
SMQ and the Barracuda App Server's integrated industrial protocols provide a solid foundation for anyone designing on-premises IoT solutions. See the tutorial Designing an On-Premises IoT Solution for details.

Broker instances are created programmatically on the server using Lua Server Pages. Since SMQ initiates the connection using HTTP(S), each broker instance is set up with a unique URL, making having one broker instance per customer easy and convenient. Isolating broker instances per customer greatly simplifies access control management design. Broker instances are super light, and the server can harbor any number of instances.
Click any of the images below:
SMQ Chat Demo |
Device LED Control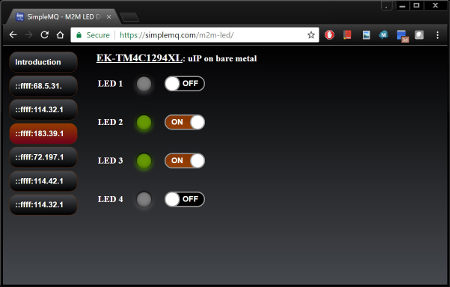
Control and supervise any number of devices from one web page, in real-time, where all connected browser windows are synchronized.
|
Weather App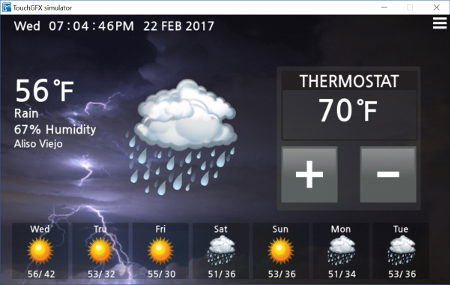
The SMQ Weather Application illustrates how a web-based user interface can be synchronized in real-time with the native user interface in a device.
|
Christmas Light Controller |
The following SMQ Weather Application video illustrates how a web-based user interface can be synchronized with the user interface in a device:
Alternatively:
You can quickly install a test broker on your own Linux computer or Windows computer using WSL as follows:
sudo -s wget http://makoserver.net/install/brokerX86/install.sh; chmod +x install.sh; ./install.sh
See the tutorial Installing The SMQ Broker On Your Own Computer for details.