If you are an embedded programmer and have found many online IoT tutorials too abstract or providing too little practical value, then the following set of tutorials may be just for you. The following hands-on articles include source code and working examples.
What is an IoT device?
An IoT device is essentially a network-connected client capable of transmitting and receiving data to and from online cloud servers. This data encompasses a wide range, from sensor readings to control messages. Various protocols facilitate these communications, including HTTP, MQTT, WebSockets, SMQ, OPC-UA and so on.
Unleash the power of the ESP32 microcontroller with our engaging Xedge32 tutorials. Designed for those who love hands-on learning, these tutorials guide you through exciting projects, from streaming ESP32-CAM images via MQTT to crafting professional embedded web interfaces. Whether you're a beginner or an expert, there's something for everyone. Dive in, experiment, and have fun while mastering the ESP32's capabilities!

MQTT Sparkplug is an extension of the MQTT protocol designed for industrial automation and control systems, providing standardized and efficient data exchange. It enables seamless integration and communication between industrial devices, edge gateways, and backend systems, focusing on real-time data exchange, device discovery, and optimized data representation.
See the tutorial Beginner's guide to MQTT & Sparkplug for a gentle introduction.
For more information and practical examples, you can refer to the GitHub repository RealTimeLogic/LSP-Examples - Sparkplug, which offers code examples and resources demonstrating MQTT Sparkplug implementation and usage in industrial automation and control systems.
Wondering which IoT service provider aligns with your needs? It's easy to gravitate towards industry giants like Amazon and Azure. While they're excellent for large-scale operations, they might be overkill for more modest projects. Plus, their services can come with a hefty price tag.
Ever thought about crafting your own IoT solution on a Virtual Private Server (VPS)? If the idea seems daunting, think again. Setting up a cost-effective IoT platform is straightforward, especially if you're open to mastering a few Linux commands. Dive into our article, Build Your Own Cost Effective IoT Platform, to explore this avenue. For starters, you can even establish an IoT learning environment on your personal computer.
Industrial machines and equipment are often deployed within private networks for security reasons. Learn how to leverage IoT within a private network by using an On-Premises IoT Platform. An On-Premises IoT Platform is installed and runs on computer(s) on the organization's premises (the private network) using the software rather than at a remote facility, such as at a cloud server on the Internet. See the article On-Premises IoT for details.
At some point, you may have to scale the IoT solution or provide redundancy. A super simple and extremely cost-effective way to scale an IoT solution is to use an IoT protocol that supports scaling by using round-robin DNS. We provide an online IoT cluster demo, including tutorials on how to set this up.
IoT and Embedded Web Server technologies have plusses and minuses. Reaping the benefits of both solutions and eliminating the negatives is possible. The article WebSockets Behind Firewall explains how this is possible.
Security is super important in IoT solutions, and all of the above tutorials incorporate the use of TLS. However, TLS is far from sufficient when it comes to securing a complete IoT solution.
The DZone article Have We Forgotten the Ancient Lessons About Building Defense Systems goes into the IoT security in detail. Did you know that it is shockingly easy to intercept local network data?
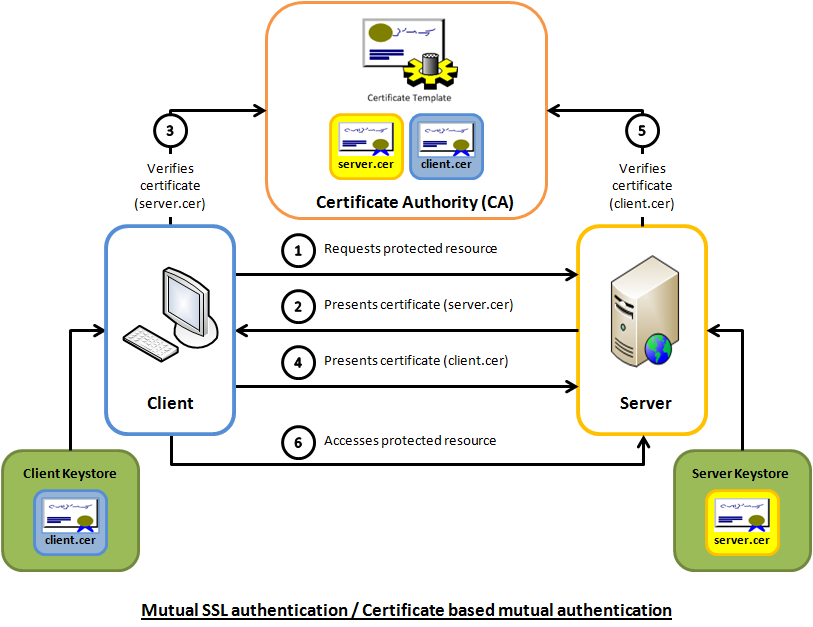
Mutual Transport Layer Security (mTLS) is a process that establishes an encrypted TLS connection in which both parties use X.509 digital certificates to authenticate each other. mTLS ensures that the parties at each end of a network connection are who they claim to be by verifying that they both have the correct private key. The information within their respective TLS certificates provides additional verification.
See the How to connect to an MQTT cloud server using Mutual TLS Authentication tutorial for details.
If so, use our ready to use one button click MQTT exploit example. The MQTT exploit is the second example on our online tutorial server. The MQTT exploit example aims to show how dangerous it is to forget to consider layered access control when designing MQTT solutions. The above DZone article goes into this in detail.
Learn the entire process of setting up the chain of trust for your IoT solution. The video, available on YouTube, provides a practical example you can follow and set up on your own computer for learning purposes. The comprehensive video tutorial guides you through the process of setting up secure and trusted communication. After completing the hands-on tutorials, you will be an expert in using SSL for secure communication and how to create and manage SSL certificates.
Check out how we rapidly designed an RTOS-powered IoT client in the following video by using an onboard web server for the development of the IoT client. The web server is initially used for powering an onboard Lua IDE, which is later disabled in the final product, where only the IoT network client is needed.
The SMQ Weather Application showcases the synchronization between a web-based user interface and the user interface of a device. The application is comprised of three components: the server application, the device (thermostat), and the browser-based user interface.
Please refer to the demo documentation for instructions on how to download the Windows demo executable and for information on how to synchronize all displays. Note that creating both a native UI and a web UI increases the cost as two separate user interfaces must be developed. However, modern web interfaces can easily replicate and provide the same user experience as any onboard UI; thus native UIs are not necessary with modern device design.
Dive deep into our treasure trove of embedded web server and IoT tutorials designed for enthusiasts like you. Yet, if deadlines loom or challenges arise, remember our experts are on standby. With Real Time Logic, you have the freedom to learn and the assurance of expert support when you need it. Let's bring your project to fruition your way.
Expedite your IoT and edge computing development with the "Barracuda App Server Network Library", a compact client/server multi-protocol stack and IoT toolkit with an efficient integrated scripting engine. Includes Industrial Protocols, MQTT client, SMQ broker, WebSocket client & server, REST, AJAX, XML, and more. The Barracuda App Server is a programmable, secure, and intelligent IoT toolkit that fits a wide range of hardware options.
SharkSSL is the smallest, fastest, and best performing embedded TLS stack with optimized ciphers made by Real Time Logic. SharkSSL includes many secure IoT protocols.
SMQ lets developers quickly and inexpensively deliver world-class management functionality for their products. SMQ is an enterprise ready IoT protocol that enables easier control and management of products on a massive scale.
SharkMQTT is a super small secure MQTT client with integrated TLS stack. SharkMQTT easily fits in tiny microcontrollers.
An easy to use OPC UA stack that enables bridging of OPC-UA enabled industrial products with cloud services, IT, and HTML5 user interfaces.
Use our user programmable Edge-Controller as a tool to accelerate development of the next generation industrial edge products and to facilitate rapid IoT and IIoT development.
Learn how to use the Barracuda App Server as your On-Premises IoT Foundation.
The compact Web Server C library is included in the Barracuda App Server protocol suite but can also be used standalone.
The tiny Minnow Server enables modern web server user interfaces to be used as the graphical front end for tiny microcontrollers. Make sure to check out the reference design and the Minnow Server design guide.
Why use FTP when you can use your device as a secure network drive.
PikeHTTP is a compact and secure HTTP client C library that greatly simplifies the design of HTTP/REST style apps in C or C++.
The embedded WebSocket C library lets developers design tiny and secure IoT applications based on the WebSocket protocol.
Send alarms and other notifications from any microcontroller powered product.
The RayCrypto engine is an extremely small and fast embedded crypto library designed specifically for embedded resource-constrained devices.
Real Time Logic's SharkTrust™ service is an automatic Public Key Infrastructure (PKI) solution for products containing an Embedded Web Server.
The Modbus client enables bridging of Modbus enabled industrial products with modern IoT devices and HTML5 powered HMIs.